... so I decided to google around for answers.
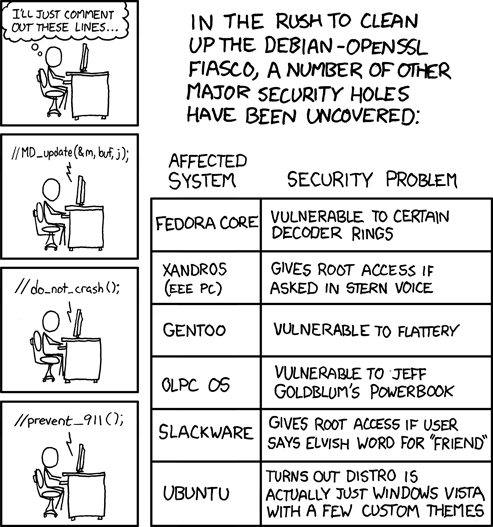
So what is this Debian-OpenSSL fiasco? I was surprised when I read that openssl's random number generator had a vulnerability that has affected the security of RSA keys since September 2006. This bug has gone unnoticed for more than a year!
However, surprise turned to shocked as I began to understand the bigger picture in layman's terms.
Instead of using random data to generate basic "seed" values for keys, the OpenSSL PRNG used the current process ID, a unique process identifier. The problem is that, in Linux, the default maximum process ID is 32,768, meaning the seed value could be overcome by brute force, or systematically applying different values in the range 0 to 32,768.
This is a security catastrophe. The experts are saying that "ANY cryptographic material created on vulnerable systems can be compromised."
3 comments:
Thanks for the interesting summary
I was curious too, so I did a Google search on "debian openssl fiasco" and this post was at the top of the results. I'm amazed because it looks like it was posted just hours ago.
Blogspot's owned by Google, so they probably index the posts immediately or something.
Post a Comment